Stop $1M Ransomware Payouts and Data Governance Collapses
Track patch management, monitor privileged access, and keep your infrastructure hardened—with or without a massive internal SOC.
DEPLOYMENT SECTOR:
CISOs • CTOs • IT Directors • Data Protection Officers (DPOs) • Heads of Risk & Internal Audit

Anatomy of an Operational Failure
*The following real-world incidents are cited based on publicly available news reports and investigation findings for educational and illustrative purposes only.*
These aren’t theoretical risks. These are real failures that shut down businesses.
The MGM & Caesars Palace Ransomware Attacks (USA, 2023)
In 2023, ransomware gangs crippled these hospitality giants not with complex hacking, but by tricking IT helpdesk staff. Our 'Phishing Simulation' SOP builds a human firewall, while our 'Incident Response' checklist provides a drilled playbook to contain an attack before it costs nine figures.
WannaCry Ransomware Attack (Global, 2017)
This global attack hit over 150 countries by exploiting unpatched systems. Our 'Patch Management' checklist ensures that all critical security patches are tested and deployed on time.
HDFC Bank Data Leak via Vendor (India, 2020)
A data leak occurred not through the bank itself, but via a third-party vendor. Our 'Vendor Security Assessment' SOP prevents this by mandating security audits for all partners.
Domino’s India Data Breach (2021)
Customer data was stolen and leaked on the dark web. Our 'Data Encryption and Access Control' SOPs ensure that even if a breach occurs, the data remains protected and useless to hackers.
A High-Gravity
Data Engine.
This is not a static PDF. You are deploying a multi-branch, logically-aware interface built to command discipline across your entire group.
Live Status Trigger
Status columns (COMPLETED/AWAITING MGR) update instantly based on staff inputs.
The 'Yellow Target' Rule
Managers only focus on highlighted high-risk points. No time wasted on routine ticks.
Institutional Memory
Trainer notes and consequences are embedded into every task to coach staff automatically.
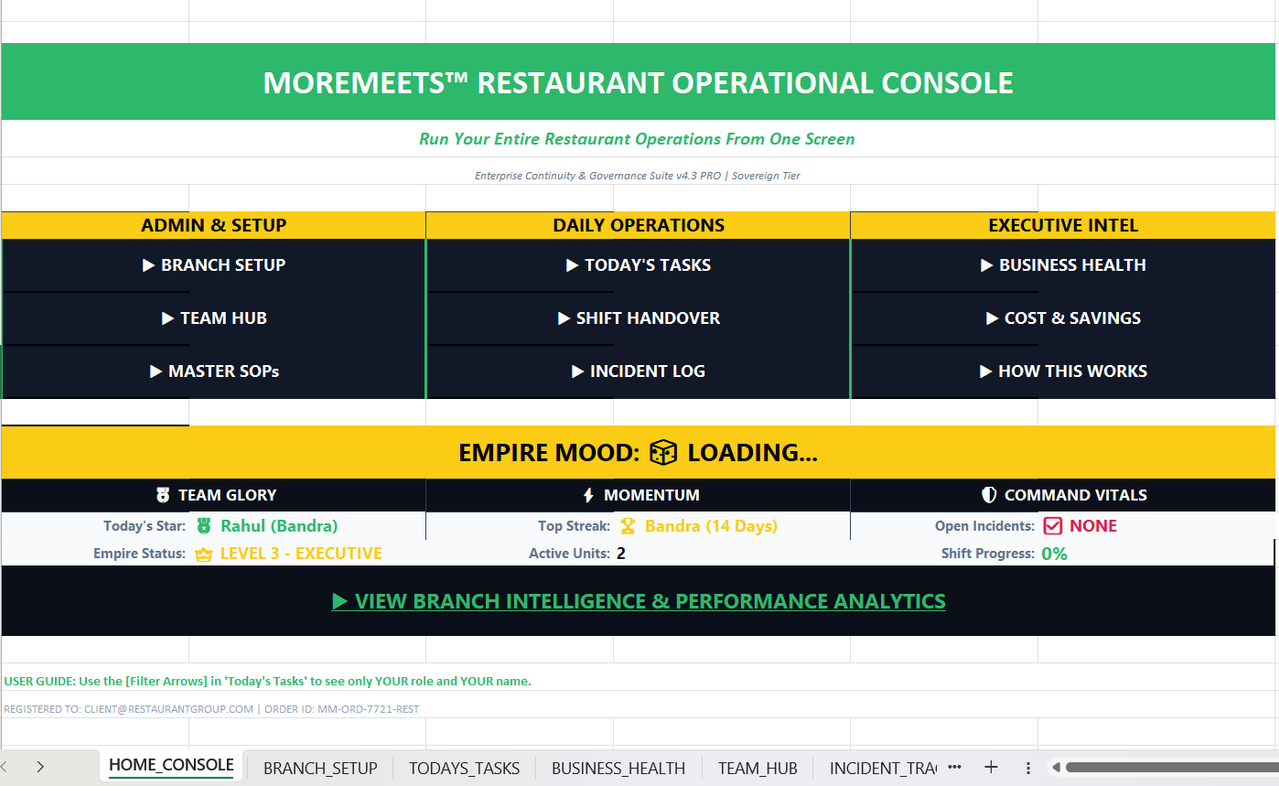
THE SYSTEM SUPERPOWERS
You are deploying a standalone data engine designed to run your business without chaos. This is what changes on Day 1:
2-Minute Security Pulse: IT teams update patch and vulnerability status in seconds. Real-time defensive visibility.
Hardened Access Control: Bulletproof protocols for quarterly user reviews, MFA enforcement, and least-privilege audits.
High-Risk Verification: Highlighted 'Yellow Targets' show Security Leads exactly what needs sign-off—from firewall rules to backups.
Resilience Engine: Battle-tested playbooks for Incident Response and Disaster Recovery to contain the 'Blast Radius'.
Institutional Memory: Capture cybersecurity 'know-how' so that your defensive standard remains constant through staff turnover.
Third-Party Governance: A structured framework for vendor security assessments to de-risk your digital supply chain.
Sovereign Infrastructure: No recurring SaaS fees. You own your risk data and the control system forever.
This is NOT a Checklist.
NOT a PDF
Static documents get ignored. This is a live, interactive data engine.
NOT a Template
Generic lists don't stop disasters. This is forensically engineered infrastructure.
NOT Manual
No more 'guessing' if work is done. You get verifiable digital evidence.
"It is a system your team uses daily to ensure discipline never drifts."
System vs. Chaos
The difference between a growing business and a struggling one.
Manual Chaos (WhatsApp & Memory)
Staff forgets tasks
Standards are just suggestions until they are signed.
You chase staff
Managers spend hours daily following up on basic duties.
No visibility
Failures are only noticed when a guest complains.
Problems caught late
Profit leaks are hidden in daily inefficiencies.
MoreMeets™ Operating System
Tasks tracked daily
Every step is signed off. Discipline becomes mandatory.
You see updates instantly
Know exactly who is performing in 5 seconds.
Full Executive Clarity
Knowledge stays with the business if staff leave.
Problems caught early
The system flags errors before they cost money.
What changes after deployment?
From firefighting to focused growth.